A compromised identity is now the #1 attack vector behind data breaches. According to IBM’s Cost of a Data Breach report, stolen credentials and identity-related attacks account for the majority of breach entry points, and the average cost of a breach now exceeds $4.88 million globally.
If you’re evaluating identity access management tools right now, you’re in the right place. We’ve analysed the top-ranking solutions, mapped them against real-world deployment scenarios in Indian and global enterprises, and highlighted exactly where each tool wins and where it falls short.
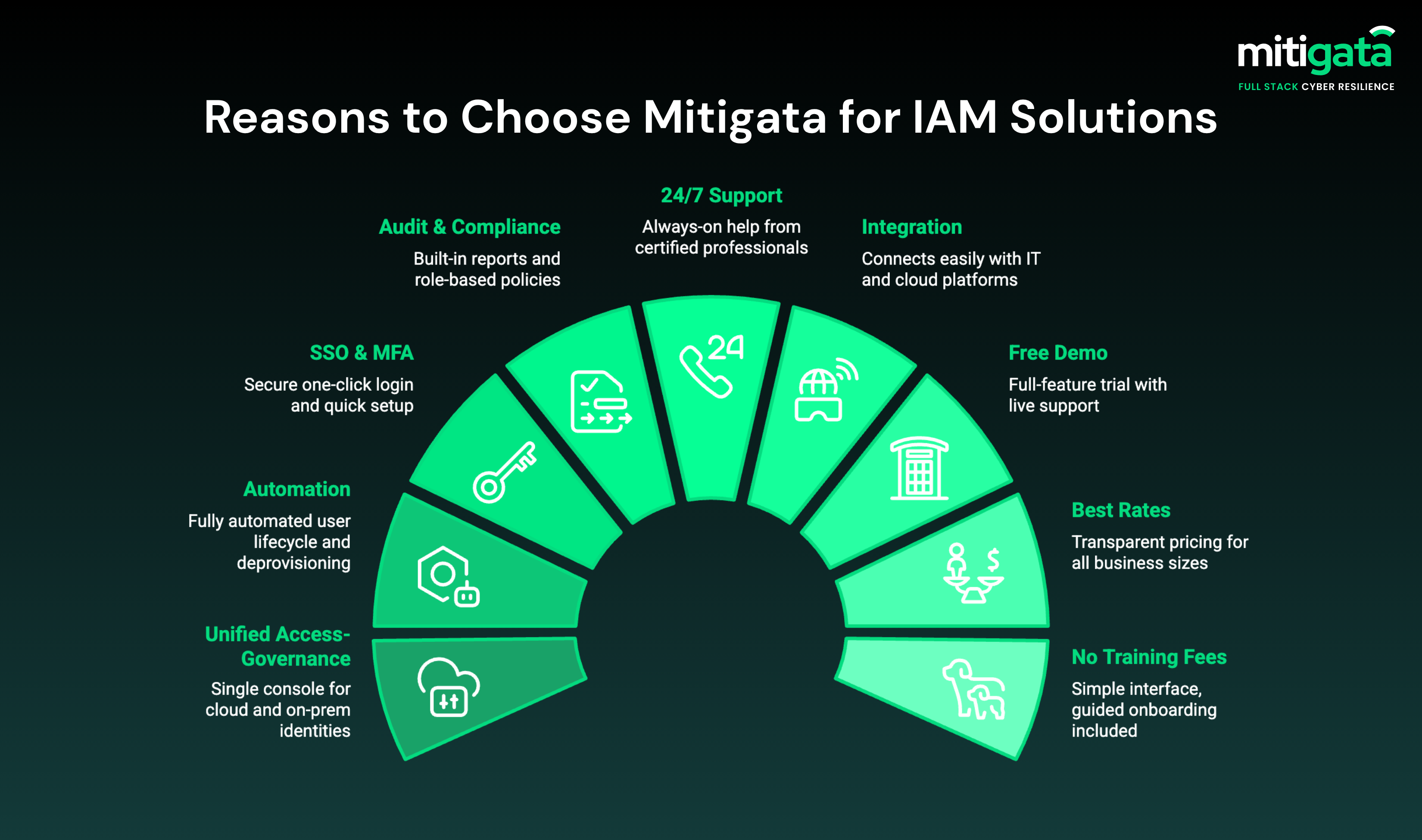
Why Businesses Choose Mitigata for IAM Services
Mitigata is India’s #1 cyber resilience platform, partnered with all major IAM OEMs. We help 800+ businesses across 25+ sectors get the right IAM tool at the best market rates, with 24/7 expert support.
What do you get with us:
- Unified access-governance platform
- Automation of user lifecycle & deprovisioning
- Single sign-on (SSO) + strong MFA + smooth onboarding
- Audit-ready reporting + role-based policy templates + compliance tracking
- 24/7 support from experienced professionals
- Smooth integration with existing security systems
- Free demo
- Best market rates
- No extra training fees
IAM Tool Categories: Know What You Actually Need
Not all identity and access management solutions solve the same problem. Before shortlisting vendors, align on which category fits your gap:
- Workforce IAM: Controls employee and contractor access across SaaS, cloud, and on-prem apps. (Okta, Entra ID)
- Customer IAM (CIAM): Manages secure authentication for customer-facing applications. (Okta Customer Identity, ForgeRock)
- Privileged Access Management (PAM): Protects admin accounts, service accounts, and high-risk credentials. (CyberArk)
- Identity Governance & Administration (IGA): Automates access reviews, provisioning workflows, and compliance reporting. (SailPoint, Omada)
- Cloud Infrastructure Entitlement Management (CIEM): Right-sizes cloud permissions in AWS, Azure, GCP environments.
Don’t fall for email traps. Read our guide on common phishing attacks and how to prevent them.
Top 7 Identity and Access Management Tools for 2026
The following are the best IAM tools that are adopted by top teams to manage permissions,
Microsoft Entra ID (previously Azure AD)

Microsoft Entra ID is the world’s most widely deployed identity and access management tool, protecting over 600 million users. It excels in environments already invested in the Microsoft ecosystem, offering deep integration with M365, Teams, SharePoint, and Azure services.
Key Features:
- Single Sign-On (SSO): One secure login across all apps using SAML, OAuth, and OpenID Connect
- Conditional Access: Risk-based access policies triggered by user location, device compliance, and sign-in patterns
- Privileged Identity Management (PIM): Time-limited, monitored admin access to eliminate standing privileges
- Identity Governance: Automated access reviews, entitlement management, and lifecycle workflows
- Hybrid Directory Sync: Seamlessly bridges on-premises Active Directory with cloud identity
- External Identities: Secures access for partners, vendors, and guest users (B2B) and customers (B2C)
Deploy Microsoft Entra ID through Mitigata for simplified licensing, faster activation, and 24/7 support.
Simplify Identity and Access Management with Mitigata
Trusted by 800+ companies, Mitigata delivers cost-effective IAM with end-to-end implementation, easy integrations, and 24/7 support.

Okta Identity Cloud

Okta is the gold standard for cloud-native workforce identity. Its Integration Network connects to 7,000+ pre-built app integrations, making it the fastest path to SSO for organisations running multiple SaaS tools. It’s particularly strong for companies that don’t want to be locked into a single vendor ecosystem.
Key Features:
- Universal Directory: Centralises user profiles from multiple identity sources (AD, LDAP, HR systems)
- Adaptive MFA: Context-aware verification adjusting challenge levels based on device, IP, and behaviour
- Lifecycle Automation: Automatically provisions and deprovisions users across all connected apps
- API Access Management: Secures API calls with OAuth 2.0 and fine-grained access policies
- Zero Trust Access: Continuous verification for every access request, regardless of network location
- Okta AI: Risk-based policy recommendations powered by identity intelligence
Get Okta Identity Cloud at exclusive Mitigata rates with expert onboarding support.
CyberArk Identity Security Platform

CyberArk is the undisputed market leader for Privileged Access Management (PAM). While it also offers workforce IAM, its core strength lies in securing the identities with the highest blast radius – admins, developers, service accounts, and increasingly AI agents.
Key Features:
- Least Privilege Enforcement: Just-in-time access elevation with zero standing privileges
- Session Recording & Monitoring: Full audit trail of privileged sessions with anomaly detection
- Secrets Management: Centralised vault for API keys, certificates, and service account credentials
- AI-Driven Governance: Machine learning accelerates access reviews and flags policy violations
- Machine Identity Security: Governs bots, service accounts, and automation credentials
AI Agent Controls: Extends identity governance to agentic AI tools running in enterprise workflows
Get CyberArk at the best market rates through Mitigata, with expert deployment and 24/7 support.
Ping Identity

Ping Identity is the IAM platform of choice for large enterprises managing complex identity flows across employee, partner, and customer populations. Its strength is protocol breadth, supporting SAML, OAuth, OpenID Connect, WS-Federation, and LDAP, making it highly interoperable with legacy and modern systems alike.
Key Features:
- Identity Orchestration: No-code visual builder for complex authentication and registration flows
- Adaptive Access Policies: Real-time risk scoring to dynamically adjust access controls
- Passwordless Authentication: FIDO2, biometric, and push-based login without passwords
- Enterprise Workstation MFA: Extends MFA to VPN, Windows, and Mac workstation logins
- PingOne DaVinci: Low-code orchestration across the entire identity journey
- Directory & Provisioning: Native SCIM and LDAP support for seamless HR-to-IT provisioning
Deploy Ping Identity with Mitigata’s certified implementation team. Book your free demo now.
Modern IAM Built for Growing Businesses
Cost-effective IAM trusted by 800+ organisations, with seamless deployment, end-to-end support, and no hidden training costs.

RSA ID Plus

RSA ID Plus delivers enterprise-grade IAM across cloud, hybrid, and fully on-premises environments. It’s the go-to for organisations in banking, defence, or critical infrastructure where data residency and deployment flexibility are non-negotiable.
Key Features:
- Risk-Based Authentication: Dynamically adjusts security checks based on real-time user behaviour and context
- Hardware and Software MFA: Supports RSA SecurID tokens, push notifications, and biometrics
- SIEM Integration: Feeds identity events into your SIEM for centralised threat detection
- Identity Governance: Automates access certification and compliance reporting workflows
- Hybrid Deployment: Full control over where identity data lives such as cloud, on-prem, or private cloud
Buy RSA ID Plus via Mitigata to unlock expert-backed support, smooth integration, and the most cost-effective pricing plans.
ManageEngine AD360
ManageEngine AD360 is the most accessible, comprehensive IAM tool for organisations running Windows Active Directory, Microsoft 365, or Exchange. It delivers lifecycle management, RBAC, MFA, SSO, and audit reporting at a fraction of the cost of enterprise platforms, making it the top choice for Indian SMBs and mid-market organisations.
Key Features:
- Unified User Lifecycle: Automates provisioning and de-provisioning across AD, M365, and Exchange from a single console
- Password Self-Service: Reduces helpdesk load with secure password reset and account unlock
- Role-Based Access Control: Enforces least-privilege policies across Windows environments
- MFA & SSO: Supports 15+ authenticators and 100+ enterprise app integrations
- Compliance & Audit Reports: Pre-built reports for SOX, HIPAA, PCI DSS, and GDPR compliance
Deploy ManageEngine AD360 through Mitigata for the best pricing and local support.
SailPoint Identity Security Cloud
SailPoint is the IGA leader, purpose-built for organisations where compliance, access reviews, and governance workflows are the primary drivers. Its AI layer – Atlas automates role management, detects toxic access combinations, and accelerates audit preparation significantly.
Key features:
- AI-Powered Access Reviews: Automated certification campaigns with intelligent recommendations
- Role Management: AI-generated role models based on actual access patterns
- Separation of Duties (SoD): Detects and prevents conflicting access that violates compliance policies
- Non-Human Identity Governance: Full lifecycle management for machine and service accounts
- Compliance Reporting: Pre-built templates for SOX, HIPAA, GDPR, and ISO frameworks
Top Identity Management Tools
Comparison
Use this table to shortlist the best IAM tools based on your environment, team size, and budget:
| IAM Tool | Best For | Key Strength | Ideal Company Size |
|---|---|---|---|
| Microsoft Entra ID | Microsoft / hybrid environments | Deep M365 & Azure integration | Mid to large enterprise |
| Okta Identity Cloud | Cloud-first SaaS environments | 7,000+ app integrations | SMB to enterprise |
| CyberArk Identity Security | Privileged access security | Industry-leading PAM | Large enterprise |
| Ping Identity | Hybrid & legacy IAM | Strong federation & identity APIs | Large enterprise |
| RSA ID Plus | High-assurance authentication | Flexible MFA deployment | Regulated industries |
| SailPoint Identity Security | Identity governance (IGA) | AI-driven lifecycle management | Enterprise |
| ManageEngine AD360 | Active Directory environments | Affordable all-in-one IAM | SMB to mid-market |
Which IAM Tool Is Right for Your Business?
The “best” identity access management tool depends entirely on your environment. Here’s a scenario-based decision guide:
| Your Situation | Best-Fit IAM Tool |
|---|---|
| You run Microsoft 365 or Azure | Microsoft Entra ID |
| Cloud-first with 50+ SaaS apps | Okta Identity Cloud |
| Admins or DevOps needing privileged access | CyberArk |
| Need compliance audit trails (SOC 2, ISO 27001, RBI) | SailPoint or ManageEngine AD360 |
| Growing SMB needing cost-effective IAM | Mitigata + ManageEngine AD360 or Entra ID |
| Hybrid mix of legacy and cloud apps | Ping Identity |
Simplify IAM Integration Across Cloud and On-Prem Systems
Secure identities across your organisation with a solution that’s easy to integrate and simple to manage.

Conclusion
Leaders like Okta, Microsoft Entra ID, CyberArk, Ping Identity and RSA ID Plus continue to set the standard with strong authentication, access governance and threat prevention capabilities. The best identity and access management tools for your business depend on your environment, user flows and security maturity.
Mitigata can help you access these industry-leading IAM softwares at discounted rates, along with guidance to ensure you pick the right fit.
Contact Mitigata today for your free IAM demo!
Frequently Asked Questions (FAQs)
What is the difference between IAM and PAM?
IAM (Identity and Access Management) governs all user identities and their access across your organisation. PAM (Privileged Access Management) is a specialised subset of IAM focused specifically on high-risk accounts, including admins, DevOps, and service accounts. CyberArk leads in PAM; Okta and Entra ID lead in broader workforce IAM.
Is IAM software suitable for small businesses?
Yes. Tools like ManageEngine AD360 and Microsoft Entra ID (bundled with M365 Business Premium) offer full IAM capabilities at SMB-appropriate price points. Even a 50-person company benefits from SSO, MFA, and automated offboarding to prevent credential-based breaches.
How long does IAM implementation take?
A basic SSO and MFA rollout can go live in 2–4 weeks. Full lifecycle management, IGA workflows, and privileged access controls typically take 3–6 months for large enterprises. Mitigata’s phased implementation approach helps organisations realise security value quickly without disrupting operations.
What compliance frameworks does IAM support?
Most enterprise IAM platforms support SOC 2, ISO 27001, GDPR, HIPAA, PCI DSS, and SOX out of the box. For India-specific mandates – RBI Cybersecurity Framework, SEBI CSCRF, and the DPDP Act. Mitigata provides compliance mapping as part of the implementation engagement.

