In 2026, the cyber world is undergoing a major shift, particularly within India’s rapidly expanding digital economy, which is racing towards the $1 trillion milestone.
The way companies build, sell, and scale online has changed fast. So have the threats. Phishing attacks are being powered by AI at scale, making them faster, smarter, and harder to detect
Attacks that once targeted only large enterprises are now hitting startups, creators, and mid-sized businesses with equal force.
Data breaches are more expensive than ever, with the average cost of a data breach in India reaching an all-time high of ₹22 Crore according to IBM’s latest analysis. And customers are paying close attention to how well you protect their trust.
This blog breaks down the cybersecurity trends for 2026 and explains how businesses can stay ahead of these changes.
Mitigata – India’s Full-Stack Cyber Resilience Company
More than 800 businesses across 25+ industries rely on us to protect them from the most common threats in today’s world.
As India’s only full-stack cyber resilience company, Mitigata offers comprehensive insurance policies, access to 500+ security products, 24/7 SOC monitoring, rapid incident response, and intelligent threat detection to keep your business secure.

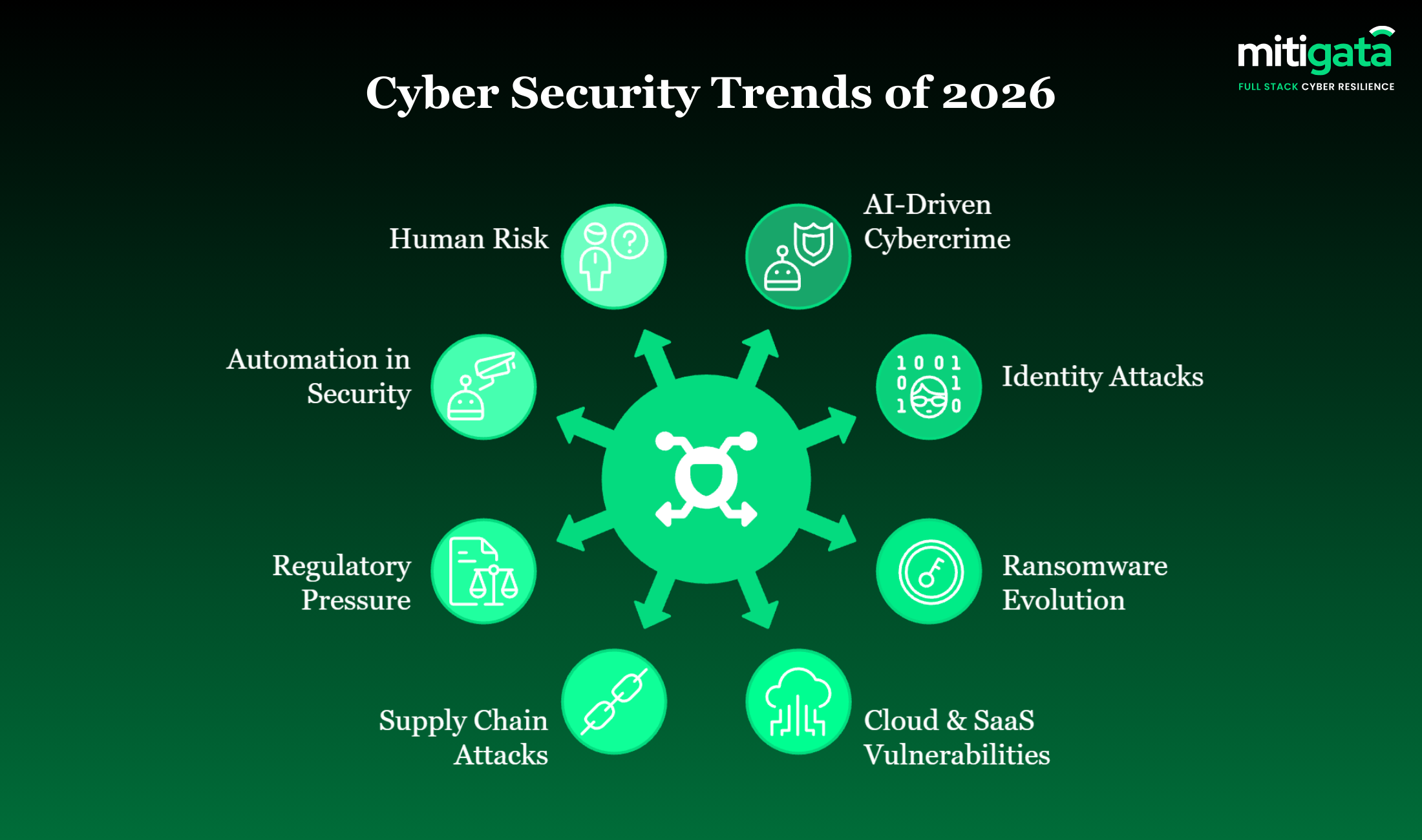
Security Trends for 2026
2026 will redefine cybersecurity as AI-powered threats, identity misuse, and cloud exposure reshape how digital businesses must defend themselves.
AI-Driven Cybercrime Goes Mainstream
Now, artificial intelligence helps the attackers to scale phishing, malware production, and attack reconnaissance at a rapid pace
It is predicted that in 2026, cybercriminals will make extensive use of AI to automate social engineering, generate undetectable malware, and orchestrate simultaneous attacks.
For example, we are seeing a rise in ‘Deepfake’ CEO fraud, where attackers use voice cloning to trick finance teams at mid-sized Indian firms into transferring funds.
In addition, AI tools can now translate phishing emails into flawless regional languages, making scams targeting Tier-2 and Tier-3 city businesses far more convincing.
For businesses, this leads to higher attack volumes and phishing attempts that are hard to detect, and increased risk of breaches that slip past traditional security controls.
Most companies buy SIEM blindly. These use cases show what it actually protects against today.
Identity Attacks Take Over Perimeter Breaches
There is a shift where attackers are now targeting more towards distributed networks and identities rather than firewalls
Compromised credentials, session hijacking, and privilege misuse are becoming the main entry points for breaches.
With the surge in remote work across Indian tech hubs, attackers are bypassing VPNs by stealing session cookies – a technique that renders Multi-Factor Authentication (MFA) less effective if not configured correctly.
In a cloud-centric environment, identity has practically become the new security perimeter.
As attackers focus on credentials rather than networks, businesses face a higher risk of account takeovers and unauthorised access in 2026.
Passwords fail daily. These identity and access management tools explain how modern security survives today.
Ransomware Moves From Encryption to Extortion
Nowadays, attackers do not lock up the systems; rather, they concentrate on getting hold of sensitive data.
Modern ransomware attacks are targeting sensitive data rather than systems, pressuring businesses through public exposure and compliance risks.
This “Double Extortion” tactic is particularly damaging for Indian SMEs, where 70% of breached organisations report significant operational disruption.
Even organisations with strong backups may suffer reputational damage, legal penalties, and customer churn following data leaks.
Personalised SIEM services Starting at just ₹6,00,000/Yearly*
Our solutions adapt to your risks, workflows, and industry needs, giving you smarter coverage without any overpromises.

Cloud and SaaS Are the Main Attack Surfaces
Cloud service providers and SaaS applications are now among the most attacked environments.
Poorly configured settings, problematic APIs, and uncontrolled SaaS applications provide hackers with a straightforward path to accessing critical company data.
This is often due to “Shadow IT”, where employees sign up for unapproved tools using company emails, leaving gaping holes in the security posture.
Companies that use multi-cloud services and those with remote employees face a greater lack of visibility.
A simple misconfiguration in an AWS S3 bucket or an Azure permission setting can expose millions of customer records instantly.
Using cloud apps blindly? These CASB companies in India reveal who protects data best today.
Supply Chain Attacks on the Rise
Cybercriminals are increasingly exploiting trust in vendors and third-party software to simultaneously breach multiple organisations’ networks.
A compromised supplier may put hundreds of businesses at risk; therefore, supply chain security will be the main concern in 2026.
Consider the interconnected nature of India’s UPI and fintech ecosystem; a single vulnerability in a payment gateway partner can cascade down to thousands of merchants.
When attackers compromise vendors or software providers, businesses can be breached indirectly without any internal weakness.
This creates operational disruptions, compliance issues, and greater dependency on third-party security posture.
Regulatory Pressure and Disclosure Expectations Rise
Governments and regulators are imposing stricter rules on cybersecurity disclosure and compliance.
Most notably, the full enforceability of the Digital Personal Data Protection (DPDP) Act creates a new compliance baseline for every Indian business handling personal data.
Companies will have to report breaches within shorter time frames, pay bigger fines, and will be scrutinised more regarding their security readiness. Stricter regulations require faster breach reporting and stronger security controls.
Businesses that fail to meet these expectations risk fines, legal action, and loss of customer confidence due to delayed or incomplete disclosures.
Smart and Cost-Effective PAM Solutions by Mitigata
Trusted by 800+ businesses, our PAM services combine cost efficiency with real-time access and complete visibility.

Human Risk Remains a Primary Entry Point:
Phishing clicks, poor passwords, and a lack of security awareness remain reasons for a good share of successful breaches even in well-established organisations.
Attackers are increasingly using “Hinglish” and context-specific lures related to tax filings or festive sales to trick Indian employees.
Employee actions such as phishing clicks and weak passwords continue to enable successful attacks.
Without continuous awareness and monitoring, human error can lead to data loss, financial fraud, and prolonged security incidents.
Why regular cybersecurity training for employees helps avoid common attacks and mistakes.
How to Prepare For Cyber Threats in 2026
Here’s a quick summary of how businesses can prepare for key security challenges in 2026.
| Security Trend for 2026 | Preparation Strategy |
| AI-driven cyber attacks | Use behaviour-based detection, continuous monitoring, and cross-platform visibility |
| Identity-based attacks | Monitor login and session activity, limit privileges, and track access movement |
| Ransomware and data extortion | Isolate backups, detect early lateral movement, and monitor data transfer |
| Cloud and SaaS security risks | Review permissions, track misconfigurations, and monitor API usage |
| Supply chain attacks | Limit vendor access, monitor third-party activity, and validate integrations |
| Regulatory and compliance pressure | Maintain audit logs, test incident response readiness |
| Security automation adoption | Automate alert triage, apply response playbooks with expert oversight |
| Human risk and social engineering | Track user behaviour, detect phishing actions, and control access |
Your Full Cyber Defence Starting at Just ₹2,00,000/Month
800+ companies trust us to run their cybersecurity with our All-in-one SOC, which offers real-time monitoring and easy integration.

Conclusion
In 2026, cyber crimes are evolving faster than ever, driven by AI-powered attacks, identity misuse, and expanding cloud environments.
To stay secure, businesses must move beyond reactive defences and adopt proactive security strategies that can protect their revenue before threats turn into losses.
Whether it is complying with the new DPDP mandates or securing your cloud infrastructure, the cost of inaction is now far higher than the cost of prevention.
Contact Mitigata today to strengthen your cyber defence and protect your business before threats impact growth.

