Security teams in 2025 face over 10,000 alerts every single day. Left unmanaged, that volume does not just create inefficiency; it creates the gaps that attackers exploit. Two of the most important components in any mature cybersecurity programme are SIEM and SOC.
They are frequently mentioned in the same breath, often confused with each other, and almost universally misunderstood.
SIEM is a technology platform. SOC is a team of people. One collects and analyses security data; the other acts on it. They are not alternatives, they are partners.
This guide explains what SIEM and SOC are, how they differ across key dimensions, how they work together in practice, and how to decide what your organisation needs right now.
Mitigata – India’s Leading SIEM Implementation Partner
Many organisations spend months reviewing SIEM platforms, only to face delays, poor implementation results, and slow vendor support.
Mitigata eliminates these challenges. With 800+ businesses relying on us across India, we bring the best SIEM solutions at the best market rates due to our partnership with leading OEMs.
Why teams prefer Mitigata:
- End-to-end execution, from assessment to full deployment.
- Configurations shaped around your industry’s needs.
- Smooth integration across your existing infrastructure.
- Transparent, market-competitive pricing with no hidden charges.
- Reliable post-deployment assistance that stays consistently available.
Complete SIEM Coverage at The Best Market Rates
We simplify the tech, secure your stack, and support you 24/7—just ask our 800+ happy clients.

SIEM and SOC: The Core Distinction in One Line
SIEM is the technology – it collects, analyses, and alerts. SOC is the team – it investigates, decides, and responds. SIEM gives the SOC its eyes. The SOC gives the SIEM its purpose. Neither works at its best without the other.
What is SIEM
Security Information and Event Management (SIEM) is a software platform that acts as the central nervous system of an organisation’s security infrastructure.
It continuously ingests log and event data from across your entire IT environment, such as firewalls, endpoints, servers, cloud platforms, applications, identity providers, and analyses it in real time to detect suspicious activity and potential threats.
The term SIEM combines two older concepts: Security Information Management (SIM), which focused on log storage and compliance reporting, and Security Event Management (SEM), which focused on real-time threat detection.
Modern SIEM platforms do both and increasingly incorporate AI, machine learning, and UEBA (User and Entity Behaviour Analytics) to detect threats that rule-based systems would miss.
Are you part of the 60% of teams still managing compliance manually? It may be time to explore India’s leading automated GRC platforms.
The rise in ransomware, phishing, and lateral movement across the enterprise has also made SIEM necessary, enabling teams to make informed security decisions rather than relying on guesswork.
Key Ways SIEM Improves IT Security Operations
Read the following ways in which SIEM enhances IT security operations through automated workflows.
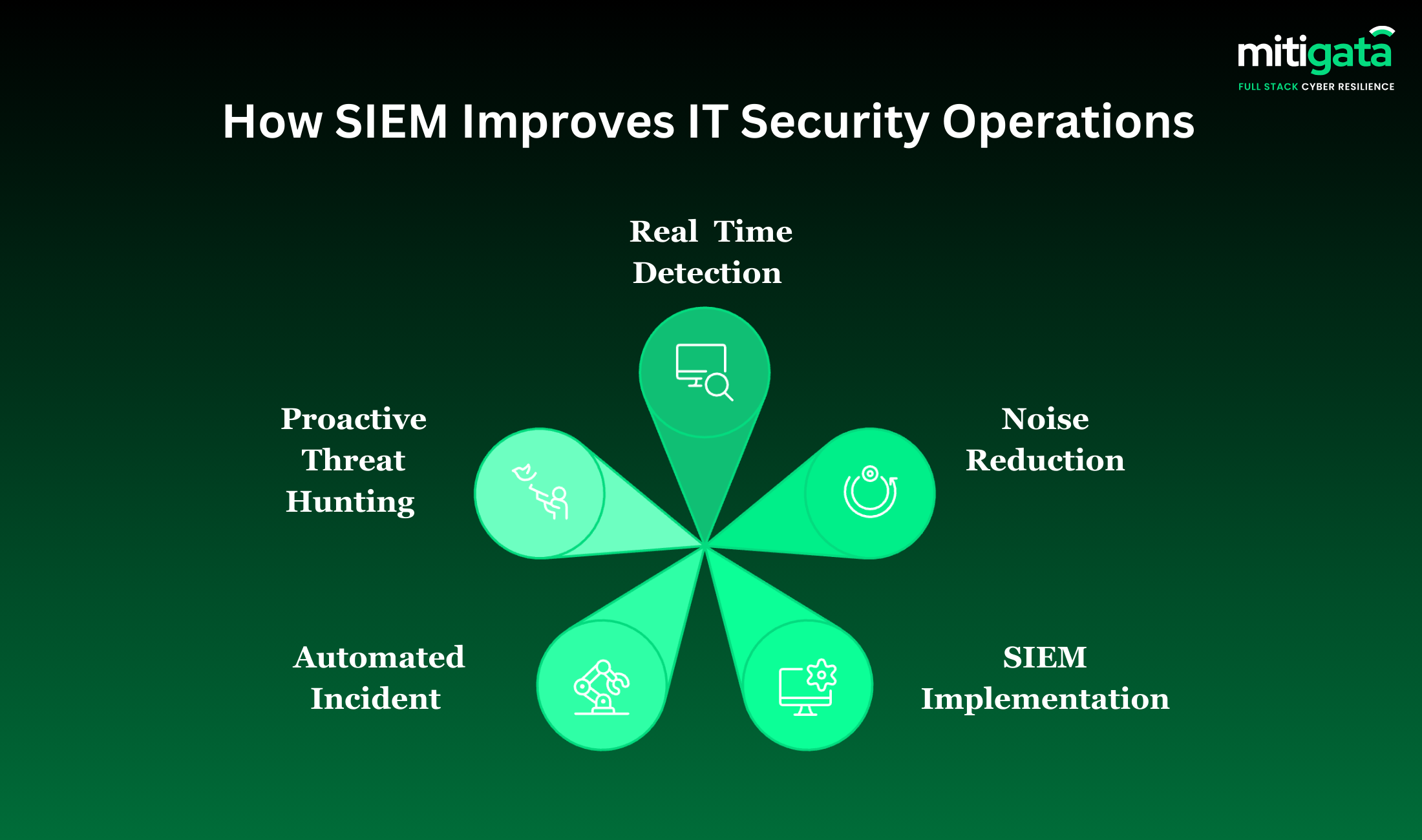
Systematic Detection of Security Events in Real-Time
By correlating events from multiple sources, the SIEM connects signals that might otherwise be missed. For example, repeated failed login attempts combined with unusual network traffic or unexpected privilege escalation.
User and entity behaviour analytics add more context by identifying actions that fall outside normal patterns. By filtering noise and highlighting genuine threats, a SIEM improves detection accuracy and significantly reduces false alerts.
Noise Reduction and Alert Management
One of the main issues in most SOCs is that repetitive, low-value alerts exhaust the SOC team. The SIEM tool enables analysts to focus on the most critical incidents. This prioritisation feature assesses alerts based on their severity, asset importance, and behavioural context.
Seeking for the top SIEM vendors in India. Our In- depth of the top 10 SIEM providers can help you make an informed choice.
One Dashboard. Zero Blind Spots.
Mitigata’s SIEM solutions give you complete visibility without complex setup or hidden costs.

Automated Incident
SIEM incident response functions are often seen to be associated with the SOAR platforms. For instance:
- Isolating an endpoint
- Disabling a compromised user account
- Blocking a malicious IP address
- Running a forensic collection script
- Sending tickets or messages to assigned responders.
Proactive Threat Hunting
It plays a major role in threat hunting. When the event history spanning several months or years is stored in a single location, analysts can perform searches that reveal hidden threats.
The use of behaviour analytics makes these searches more comprehensive. A single insignificant or routine activity is part of a larger pattern when viewed alongside other data points.
What is a SOC?
A Security Operations Centre (SOC) is a dedicated team and often a physical or virtual space of cybersecurity professionals responsible for the continuous monitoring, detection, analysis, and response to security incidents across an organisation.
Unlike SIEM, which is a tool, a SOC is a human function: people, processes, and technology working in an integrated operation.
The SOC is the organisation’s frontline defence against cyberattacks. SOC analysts receive alerts from tools like SIEM, investigate them, determine their severity, and take action, from closing a false positive to initiating a full incident response procedure that might involve isolating systems, notifying regulators, and coordinating with law enforcement.
SIEM vs SOC: Key Differences Explained
Here is a comprehensive comparison across every dimension that matters for understanding how SIEM and SOC differ and why that distinction shapes your security investment decisions:
| Dimension | SIEM | SOC |
|---|---|---|
| What is it? | A software platform/technology | A team of cybersecurity professionals |
| Primary function | Collect, analyse, and alert on security data | Monitor, investigate, and respond to security incidents |
| Operates on | Log and event data from the IT infrastructure | SIEM alerts, threat intelligence, and endpoint telemetry |
| Response capability | Generates alerts; limited automated containment (with SOAR) | Full incident response: containment, eradication, recovery |
| Works 24/7 automatically? | Yes, software runs continuously | Requires shift staffing to achieve 24/7 coverage |
| Handles context and judgment? | No, rule and algorithm-based only | Yes, human analysts interpret business and threat context |
| Threat hunting capability | Stores data for forensic queries; supports hunting | Actively hunts using SIEM data and other telemetry |
| False positive handling | Cannot distinguish; generates alerts regardless | Tier 1 analysts triage and validate alerts |
| Compliance reporting | Automated log retention and report generation | Uses SIEM reports; provides audit support and documentation |
| Cost structure | Software licence + infrastructure (₹5L–₹50L/yr for SMEs) | Staffing + tools (₹20L–₹2Cr+/yr for in-house SOC) |
| Outsourceable? | Yes, managed SIEM services available | Yes, SOCaaS / MSSP models widely available in India |
| Can it work without the other? | Yes, but alerts go unacted on | Yes, but analysts lack visibility and detection speed |
How SIEM and SOC Work Together
The power of SIEM and SOC is not in either individually; it is in their integration. Together, they form a continuous security loop that covers detection, analysis, response, and improvement in a cycle that constantly strengthens over time.
| Step | Who Acts | What Happens |
|---|---|---|
| Data Ingestion | SIEM | SIEM continuously pulls in logs from firewalls, endpoints, servers, cloud platforms, identity providers, and applications across the entire IT environment |
| Normalisation & Correlation | SIEM | Raw logs are normalised into a standard format. SIEM’s correlation engine cross-references events across sources, connecting individual signals into meaningful patterns |
| Threat Detection & Alerting | SIEM | When a pattern matches a detection rule, threat intelligence indicator, or UEBA anomaly, SIEM generates an alert with severity scoring and contextual metadata |
| Alert Triage | SOC Tier 1 | SOC analyst receives the SIEM alert. Validates whether it is a genuine threat or false positive using additional context — user history, asset criticality, threat intelligence enrichment |
| Investigation | SOC Tier 2 | For confirmed or suspected incidents, Tier 2 analyst conducts deep investigation: queries SIEM logs, reviews endpoint telemetry, maps attacker behaviour to MITRE ATT&CK framework |
| Containment & Response | SOC Tier 2/3 | SOC initiates incident response: isolates affected systems, disables compromised accounts, blocks malicious IPs, preserves forensic evidence, and notifies stakeholders |
| Eradication & Recovery | SOC + IT | The threat is removed from the environment. Affected systems are restored. Root cause analysis is conducted to understand how the attacker got in |
| Rule Refinement | SOC feeds back to SIEM | SOC analysts update SIEM detection rules based on what was learned, reducing future false positives, improving detection of similar threats, and strengthening the entire security loop |
SIEM or SOC Or Both?
The honest answer for most organisations is: both. But budget and maturity are real constraints. Here is a practical framework for deciding where to start and how to scale:
| Business Situation | Recommended Approach |
|---|---|
| Startup or very small business (under 50 employees) | Start with a managed SIEM service. Alerts can be reviewed by your IT team or an on-call MSSP. Build towards a managed SOC as you grow. |
| SME with regulatory compliance obligations (BFSI, healthcare, e-commerce handling personal data) | Managed SIEM + Managed SOC (SOCaaS) is the most cost-effective path. In-house SOC is unlikely to be economically viable at this scale. |
| Mid-market enterprise (200–500 employees) | Managed SIEM to give your existing team visibility. Consider MSSP for after-hours SOC coverage. Build towards an in-house SOC capability over 12–24 months. |
| Large enterprise or listed company (RBI, SEBI, or IRDAI regulated) | In-house SIEM with in-house or hybrid SOC is the expected standard. Regulatory frameworks effectively require 24/7 monitoring capability. |
| Business that has experienced a breach or near-miss | Immediate deployment of managed SIEM + managed SOC. A breach without detection capability makes the next breach significantly more likely. |
A practical step-by-step guide for enterprises to implement SIEM and improve visibility, threat detection, and incident response.
Conclusion
With SIEM in place, organisations gain scalable, cost-effective protection against evolving, AI-driven threats while strengthening operational efficiency and regulatory compliance.
In a threat landscape that never slows down, SIEM ensures your security team stays one step ahead.
Looking for an SIEM deployment that works smoothly? Contact Mitigata now to speak with our cybersecurity experts for free.

